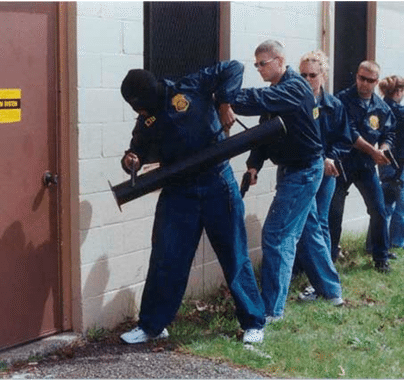
Law enforcement officers are frequently confronted with the need to gain access to something or someone. Most patrol officers don’t carry any specific “tools” for gaining entry so they must improvise by using duty boots and ASP batons as makeshift forcible entry tools. Having kicked in my fair share of doors and broken a few windows with a baton, I am the first to admit that doing so is not as easy as it looks on TV.
Circumstances often dictate how an officer will attempt to gain access to something. Is there an immediate need to gain access to save life or property? Is the officer in hot pursuit of a suspect who just ran inside of a building and locked a door? Is the officer serving a search warrant and the warrant is a “no knock warrant”, allowing for forcible entry without notifying the occupants? In some situations like high-risk search warrants and barricaded subjects, law enforcement may use forcible entry as part of their surprise, speed, and violence-of-action tactics. Other considerations for an officer making a decision about entry include department policies, the officer’s legal authority to gain access, and the amount of damage that may be caused.
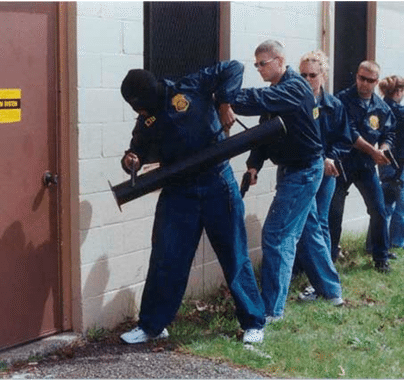
Image courtesy of Wikipedia
In other non life-threatening situations, law enforcement may need to gain access to a safe, vehicle, building, or other locked object as part of an investigation. These incidents provide additional time and options for an officer to gain access. Law enforcement may call upon the services of a locksmith to assist, look around for spare keys, contact landlords, etc. to try and gain access without forcing entry.
One common call that law enforcement responds to where access is frequently a problem is welfare checks. Officers are usually dispatched to welfare checks when a person hasn’t been heard from or seen in an unusually long time or missed an appointment. These calls come from employers who report an employee missed work unexpectedly, a family member who can’t get in contact with their loved one, the mail carrier who reports that newspapers and mail is stacking up, or the dreaded “unusual odor coming from a residence” call.
Welfare checks were never on my top-ten list of enjoyable calls to handle. It seemed to never fail that these calls would come in at night, during the graveyard shift and at the creepiest house in my beat. The standard protocol is to look for the obvious signs something is wrong; looking into any open windows for people that are dead or alive, checking for insect activity, looking at vehicles at the home for evidence they have moved recently, and talking with neighbors. Once an officer determines that more likely than not there is someone inside that may need assistance or may be deceased, they can enter the home without a search warrant under the authority of community caretaking laws.
These situations are challenging because unless the officer can see someone in distress, kicking in the door and causing damage is the last thing an agency wants. Sometimes people just leave for vacation and forget to tell anyone, or are admitted to the hospital and didn’t have time to notify their mail carrier or neighbors. For this reason, officers are trained to “try before you pry”, meaning they will check all doors, windows, and other access points to see if anything is unlocked. If nothing is unlocked and no keys can be located, the officer can try to get a locksmith to respond or make the decision to force entry to the residence.
Usually the rookie officer on the call is the lucky one who gets sent in through an opening and then has to unlock a door to let their backup officer in. It was always amusing to watch the officer walk as fast as they could to the door, without actually running. No officer wants to appear bothered by the fact that they are alone in a strange home with a possible dead or dying person that they may encounter between where they entered the home and the door to let their backup in. The officer has no idea what they are going to find from room to room. I have found deceased people sitting in their vehicle in the garage, lying in bed, on the ground somewhere within the house, and even outside in yards and sheds. The cause of death in some of my cases ranged from suicide to homicide to natural causes.
Emergency responders are trained to imagine the worst-case scenario. Mentally, this is supposed to help a first responder if they picture the worst in their mind’s eye and once on-scene are pleasantly surprised. Doing the opposite of hoping for the best but finding the worst can affect a responder’s ability to perform because they become overwhelmed due to their lack of preparation. This can affect them mentally both immediately during the incident and in the future. It is for this reason, most officers go into a welfare check expecting to find someone who died a violent death and is in advanced stages of decomposition. Then it is no big deal to find the victim recently died of apparent natural causes.
Several years ago I heard about classes being offered which taught law enforcement the art of covert entry. I was accepted into the course and learned how to successfully pick or bypass a wide variety of lock mechanisms. Having this skill caused me to get called out to assist in search warrants, welfare checks, children locked in vehicles, and other calls for service where locks needed to be accessed. Every one of these calls could be a blog entry of their own, there was never a dull moment when deploying these tools.

Standard lockpicking set – image courtesy of Wikipedia
Usually, the police want people to know they were inside of their home or business. For example, anytime the police serve a normal search warrant and there is no one present at the target location, the police must post the search warrant in a conspicuous location to notify the occupants. There are instances though where the police must access something and they don’t want anyone to know they were there. This is where “covert” entry really comes in handy.
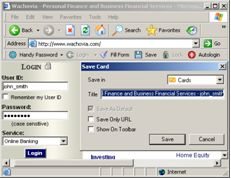
Law enforcement sometimes has the need to enter a building just to look around without actually seizing any evidence. There are instances where law enforcement may need to enter a residence or business in order to install technical surveillance measures (e.g., cameras and audio transmitters) or gather additional intelligence. These search warrants are commonly referred to as sneak and peek warrants, covert entry search warrants, and surreptitious search warrants. Law enforcement must be able to pick or bypass locks quickly and quietly in order to access these buildings without drawing any attention or leaving evidence behind of their presence.

Pocket Lockpick set – image courtesy of lockpicks.com
Covert entry techniques can also be used to save lives and property. Several years ago I overheard a radio call sending patrol units to a local hotel to check the welfare of a possible suicidal subject. After a few minutes, the patrol officers started calling for the fire department to respond to force entry into the hotel room.
I decided to respond to see if I could be of any assistance. When I arrived, several officers were standing outside of the hotel room along with the hotel manager. For some reason, the hotel manager’s key card would not open the door. The officers told me that the subject called 9-1-1 and said he had overdosed on pills. The officers also found the subject’s car still in the parking lot and were afraid for his safety.
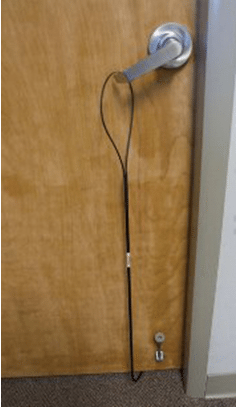
This particular hotel had the standard solid-core fire door, deadbolt locks, and a solid metal frame around the door. The hotel manager was about to authorize the fire department to actually cut a whole in the wall next to the door because it would be easier to access the room via the wall instead of trying to pry the door open. Using a specialized tool that bypasses the “L” style door handles, I was able to get the hotel room door open in about 60 seconds. As soon as the door opened, it hit the latch that had been thrown on the door. We immediately knew someone was in the room and we could hear labored breathing (agognal respirations) coming from inside. This type of breathing is commonly referred to as the “death rattle” because of its ominous sound.
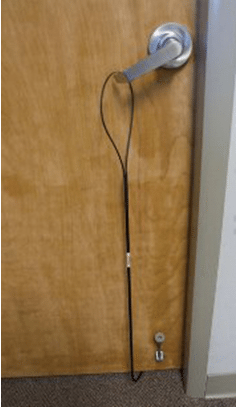
“L” handle door bypass tool. Photo courtesy of mbausa.com
My next tool in my bag of tricks was something called a Lock Jockey, which is specifically designed to bypass the hotel throw-latch. I placed this tool inside of the door and over the latch, closed the door slightly and we were in. We had no idea what to expect once we entered the hotel room. Suicidal individuals are often homicidal, so officer safety was paramount. As we went inside the room, we located the man who was completely unconscious and unresponsive. An empty pill bottle was near him and he was just a few minutes from respiratory arrest. The paramedics rushed in and began treating the man and he ultimately made a full recovery. There is no doubt that the officers and firefighters would have gained access to this man somehow, but the time it would have taken and the damage in the process would have been detrimental.

Lock Jockey tool unlatching hotel style throw-latch. Picture courtesy of lockjockey.com
* * *
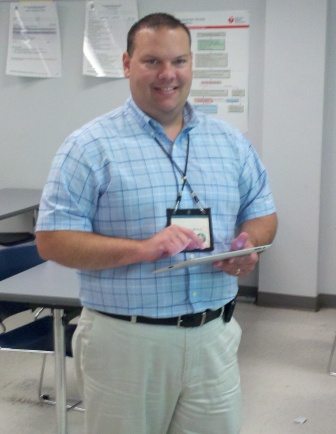
Josh Moulin has a long history of public service, beginning in 1993 as a Firefighter and EMT. After eight years of working assignments including; suppression, prevention, training, and transport ambulance, Josh left the fire service with the rank of Lieutenant when he was hired as a police officer.
Josh spent the next eleven years in law enforcement working various assignments. Josh worked as a patrol officer, field training officer, arson investigator, detective, forensic computer examiner, sergeant, lieutenant, and task force commander.
The last seven years of Josh’s law enforcement career was spent as the commander of a regional, multi-jurisdictional, federal cyber crime task force. Josh oversaw cyber crime investigations and digital forensic examinations for over 50 local, state, and federal law enforcement agencies. Under Josh’s leadership, the forensics lab was accredited by the American Society of Crime Lab Directors / Laboratory Accreditation Board (ASCLD/LAB) in 2009.
Josh has been recognized as a national expert in the field of digital evidence and cyber crime and speaks across the nation on various topics. He has testified as an expert witness in digital forensics and cyber crime in both state and federal court on several occasions. He also holds a variety of digital forensic and law enforcement certifications, has an associate’s degree and graduated summa cum laude with his bachelor’s degree.
In 2012 Josh left law enforcement to pursue a fulltime career in cyber security, incident response, and forensics supporting a national security federal agency as the Monitor and Control Team Lead. Josh also holds an active Top Secret security clearance.
Josh is happy to answer questions for authors and can be contacted at his website http://JoshMoulin.com. Josh is also on Twitter, Google+, Facebook, YouTube, and LinkedIn which can all be found on his website.